Java For Mac Os X 10.6 Update 2
- Question: Q: Can't install Java for Mac OS X 10.6 Update 10 More Less Apple Footer This site contains user submitted content, comments and opinions and is for informational purposes only.
- Apple Java for OS X 10.6 Update 2 file size: 78.12 MB Java for Mac OS X 10.6 Update 2 delivers improved compatibility, security, and reliability by updating Java SE 6 to 1.6.020.
For the protection of our customers, Apple does not disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available. To learn more about Apple Product Security, see the Apple Product Security website.
For information about the Apple Product Security PGP Key, see 'How to use the Apple Product Security PGP Key.'

Where possible, CVE IDs are used to reference the vulnerabilities for further information.
To learn about other Security Updates, see 'Apple Security Updates.'
Java for Mac OS X 10.6 Update 2
Apple Releases Updates for Java Mac OS X 10.5 and 10.6. Apple has released Java for Mac OS X 10.5 Update 7 and Java for Mac OS X 10.6 Update 2 to address multiple vulnerabilities. These vulnerabilities may allow an attacker to execute arbitrary code or cause a denial-of-service condition. And apply any necessary updates to help mitigate the risks. This product is provided subject to this Notification and this Privacy & Use policy. Java for Mac OS X 10.6 Update 2 updates Java SE 6 to 1.6.020 and is a 78MB download. Apple’s release notes: APPLE-SA-2010-05-18-2 Java for Mac OS X 10.5 Update 7. By SK 1 comment Last updated May 20, 2010. A handful of users have reported issues after applying the recently released Java for Mac OS X 10.6 Update 2. Among the reported problems: Memory leak. Apple Discussions poster Howard SOA writes: “one of my server applications suffers serious memory leak problem. The java process will simply uses up all available memory and crashes.
Java
CVE-ID: CVE-2009-1105, CVE-2009-3555, CVE-2009-3910, CVE-2010-0082, CVE-2010-0084, CVE-2010-0085, CVE-2010-0087, CVE-2010-0088, CVE-2010-0089, CVE-2010-0090, CVE-2010-0091, CVE-2010-0092, CVE-2010-0093, CVE-2010-0094, CVE-2010-0095, CVE-2010-0837, CVE-2010-0838, CVE-2010-0840, CVE-2010-0841, CVE-2010-0842, CVE-2010-0843, CVE-2010-0844, CVE-2010-0846, CVE-2010-0847, CVE-2010-0848, CVE-2010-0849, CVE-2010-0886, CVE-2010-0887
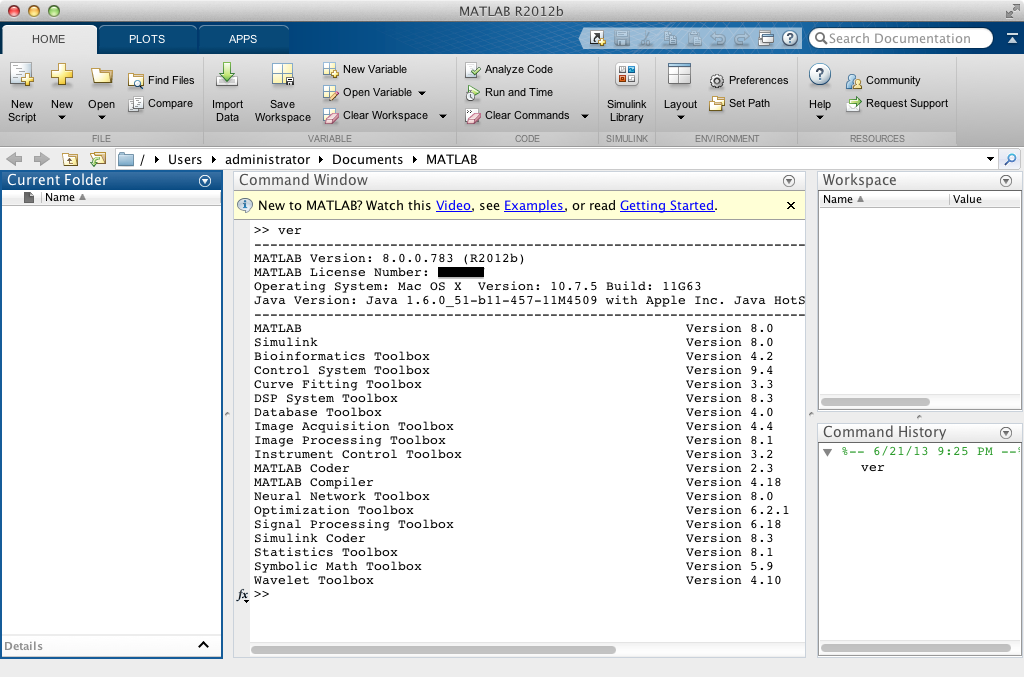
Available for: Mac OS X v10.6.3, Mac OS X Server v10.6.3
Impact: Multiple vulnerabilities in Java 1.6.0_17
Description: Multiple vulnerabilities exist in Java 1.6.0_17, the most serious of which may allow an untrusted Java applet to execute arbitrary code outside the Java sandbox. Visiting a web page containing a maliciously crafted untrusted Java applet may lead to arbitrary code execution with the privileges of the current user. These issues are addressed by updating to Java version 1.6.0_20. Further information is available via the Sun Java website at http://www.oracle.com/technetwork/java/javase/releasenotes-136954.html
Java
CVE-ID: CVE-2010-0538
Available for: Mac OS X v10.6.3, Mac OS X Server v10.6.3
Impact: Visiting a web page containing a maliciously crafted untrusted Java applet may lead to an unexpected application termination or arbitrary code execution with the privileges of the current user
Description: An out of bounds memory access issue exists in the handling of mediaLibImage objects. Visiting a web page containing a maliciously crafted untrusted Java applet may lead to an unexpected application termination or arbitrary code execution with the privileges of the current user. This issue is addressed by preventing Java applets from using the com.sun.medialib.mlib package. This issue only affects the Mac OS X implementation of Java. Credit to Marc Schoenefeld of University of Bamberg for reporting this issue.
Java For Mac Os X 10.6.8
Java
CVE-ID: CVE-2010-0539
Available for: Mac OS X v10.6.3, Mac OS X Server v10.6.3
Impact: Visiting a web page containing a maliciously crafted untrusted Java applet may lead to an unexpected application termination or arbitrary code execution with the privileges of the current user
Description: A signedness issue exists in the handling of window drawing. Visiting a web page containing a maliciously crafted untrusted Java applet may lead to an unexpected application termination or arbitrary code execution with the privileges of the current user. This issue is addressed through improved bounds checking. This issue only affects the Mac OS X implementation of Java. Credit to Jonathan Bringhurst of Northrop Grumman, and Jeffrey Czerniak for reporting this issue.
